Posted by Cliff Tuttle| March 10, 2016 | © 2026
No. 1,253
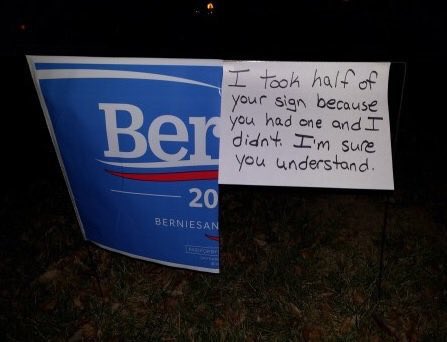
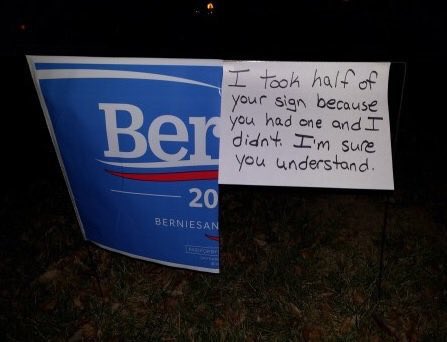
FEELING THE BER(n).
Posted by Cliff Tuttle| March 7, 2016 | © 2026
No. 1,252
COMMONWEALTH v. TALBOT S. SMITH, 2016 Pa. Super. 43.
Summary: Use of a smart phone app to record a conversation without consent of the other party is a felony.

Image: valleylearningcenter.coursestorm.com
Talbot Smith was a corporate executive who used the voice memo application on his smart phone to surreptitiously record a meeting with his boss. The existence of the recording was uncovered during discovery during civil litigation between Smith and the company following his discharge.
Smith was charged with interception of of oral communications under the Wiretapping and Electronic Surveillance Control Act, 18 Pa. C.S. § 5703.
The trial court granted the defendant’s petition for writ of habeas corpus and the Commonwealth appealed to the Superior Court.
The Superior Court noted that Section 5703 of the Wiretap Act provides that “a person is guilty of a felony of the third degree if he . . . intentionally intercepts, endeavors to intercept, or procures any other person to intercept or endeavor to intercept any wire, electronic or oral communication.” 18 Pa.C.S. § 5703(1) (emphasis supplied).
However, the statute contained an exception for:” Any telephone or telegraph instrument, equipment or facility, or any component thereof, furnished to the subscriber or user by a provider of wire or electronic communication service in the ordinary course of its business, or furnished by such subscriber or user for connection to the facilities of such service and used in the ordinary course of its business, or being used by a communication common carrier in the ordinary course of its business, or by an investigative or law enforcement officer in the ordinary course of his duties. . . .”
The trial court applied the Pa. Supreme Court’s decision in Commonwealth v. Spence, 91A3d 44 (2014). In Spence, the Supreme Court had held that the use of a telephone was exempt under the statute, regardless of “the use to which the telephone is being put.” There, the police had required a drug dealer to call a suspect with his cell phone and listened to the conversation on the speaker. No recording of the incriminating communication was made. The police simply listened.
The Commonwealth argued that in the Smith case, the voice memo app used by the Defendant was not a telephone function, but was more analogous to a pre-smart phone era tape recorder. The Superior Court agreed.
Of course, this holding, which was published on February 19, 2016, is subject to appeal to the Supreme Court.
CLT
Posted by Cliff Tuttle| February 29, 2016 | © 2026
No. 1,251
Summary: The real-life drama unfolding before us is just as exciting as House of Cards. New episodes of both will be released this week.

Image: idigitaltimes.com
Well, the next season of House of Cards will be available to binge watch once more beginning this Friday March 4. But this year it has competition. The 2016 Presidential Campaign is easily a match for any work of political fiction that there has ever been.
At this moment, Donald Trump, a living character every bit as compelling as the fictional Frank Underwood, leads the polls in most of the States voting on Super Tuesday, March 1. With a sweep he can lock up the nomination. He has broken all of the rules and somehow, they don’t matter. Opponents’ attacks do nothing to stop the jugernaut of Teflon Don 2. But what is lurking in the shadows?
On the other side, Hillary Clinton, a living character as fascinating as Frank Underwood’s wife Claire, should be riding the wave. While she has just won a smashing victory in South Carolina, the polls show that too many people regard her as duplicitous. Pesky Bernie Sanders, who literally appeared from nowhere, will not be strong enough to deprive her of the nomination. But the fissures that have been opened may well keep her from attaining the prize. Meanwhile, the FBI continues to investigate her email and she can’t shake off questions about Libya or the unchecked rise of Isis. Yet, history has taught us not to underestimate the Clintons.
The Country is mesmerized. We wait breathlessly for each new episode, while the wheel of fortune slowly turns.
CLT
Afterthought: Don’t be so consumed with politics that you miss the conclusion of Downton Abby next Sunday Night.
Posted by Cliff Tuttle| February 27, 2016 | © 2026
No. 1,250
Pittsburgh is tied for third highest cap rate for single family residences as investments among US cities. Cap rate is the ratio between net annual income and fair market value.
Read about it in DS News, an on-line publication directed to lenders, loan servicer and investors.
CLT
Posted by Cliff Tuttle| February 24, 2016 | © 2026
No. 1,249
Read the article in the Gadgeteer. The FCC is enabling cell phone carriers to set up texting to 911. Very useful if you can’t talk for any reason, from handicap to kidnapping.

Posted by Cliff Tuttle| February 22, 2016 | © 2026
No. 1,248

Image: suretech.com
I read not too long ago that most hacking of law offices occur as a result of an employee clicking on a link in an email.
Unfortunately, some of the bad guys have been getting very good at impersonation. Recently I received two emails supposedly from a well-known national retailer. The layout was impeccable — no spelling or grammar errors, excellent graphics. The first invited me to enter my name in their bridal registry. A couple hours later, a second email arrived thanking me for registering (I didn’t) and telling me that I would receive a thank you gift. Just click on the link, it said.
Of course, this was no temptation for me — but consider a 22 year-old secretary in a law firm who finds this in her morning email. Of course, the email could have been legitimate. Sometimes you just don’t know. But in a world where electronic deception is all too common, we must take care not to click on unsolicited links.
The firm should give strict instructions to its employees never to click links on any unsolicited email.
CLT
Posted by Cliff Tuttle| February 17, 2016 | © 2026
No. 1,247
Summary: Apple deserves praise from lawyers for seeking to protect our privacy. The security system which Apple refuses to compromise, helps us fulfill our ethical duty to protect client information.

Image: more.com
Lawyers, like other professionals, have an ethical duty to protect client confidential information. While we have been told that any system can be hacked, this possibility does not relieve the responsibility to take reasonable measures to prevent security breaches from occurring.
One way to protect client security is to acquire the latest generation of phones and tablets. Not only are they password protected, but they have built-in methods for destroying the data when a device is lost or stolen. This includes a security lock when someone is making repeated attempts to find the password.
This system works so well that the FBI is unable to unlock the password of the company-owned iPhone used by one of the San Bernadino shooters. The government obtained an order of court directing Apple to assist them in developing a method to unlock the iPhone. Apple says that it doesn’t have a means to perform this operation and does not wish to create one, since it could then be used by anyone as a back door into any iPhone in its hands. For lawyers, such a data breach is unacceptable.
Here is the full text of a letter Apple has published yesterday:
“February 16, 2016
A Message to Our Customers
The United States government has demanded that Apple take an unprecedented step which threatens the security of our customers. We oppose this order, which has implications far beyond the legal case at hand.
This moment calls for public discussion, and we want our customers and people around the country to understand what is at stake.
The Need for Encryption
Smartphones, led by iPhone, have become an essential part of our lives. People use them to store an incredible amount of personal information, from our private conversations to our photos, our music, our notes, our calendars and contacts, our financial information and health data, even where we have been and where we are going.
All that information needs to be protected from hackers and criminals who want to access it, steal it, and use it without our knowledge or permission. Customers expect Apple and other technology companies to do everything in our power to protect their personal information, and at Apple we are deeply committed to safeguarding their data.
Compromising the security of our personal information can ultimately put our personal safety at risk. That is why encryption has become so important to all of us.
For many years, we have used encryption to protect our customers’ personal data because we believe it’s the only way to keep their information safe. We have even put that data out of our own reach, because we believe the contents of your iPhone are none of our business.
The San Bernardino Case
We were shocked and outraged by the deadly act of terrorism in San Bernardino last December. We mourn the loss of life and want justice for all those whose lives were affected. The FBI asked us for help in the days following the attack, and we have worked hard to support the government’s efforts to solve this horrible crime. We have no sympathy for terrorists.
When the FBI has requested data that’s in our possession, we have provided it. Apple complies with valid subpoenas and search warrants, as we have in the San Bernardino case. We have also made Apple engineers available to advise the FBI, and we’ve offered our best ideas on a number of investigative options at their disposal.
We have great respect for the professionals at the FBI, and we believe their intentions are good. Up to this point, we have done everything that is both within our power and within the law to help them. But now the U.S. government has asked us for something we simply do not have, and something we consider too dangerous to create. They have asked us to build a backdoor to the iPhone.
Specifically, the FBI wants us to make a new version of the iPhone operating system, circumventing several important security features, and install it on an iPhone recovered during the investigation. In the wrong hands, this software — which does not exist today — would have the potential to unlock any iPhone in someone’s physical possession.
The FBI may use different words to describe this tool, but make no mistake: Building a version of iOS that bypasses security in this way would undeniably create a backdoor. And while the government may argue that its use would be limited to this case, there is no way to guarantee such control.
The Threat to Data Security
Some would argue that building a backdoor for just one iPhone is a simple, clean-cut solution. But it ignores both the basics of digital security and the significance of what the government is demanding in this case.
In today’s digital world, the “key” to an encrypted system is a piece of information that unlocks the data, and it is only as secure as the protections around it. Once the information is known, or a way to bypass the code is revealed, the encryption can be defeated by anyone with that knowledge.
The government suggests this tool could only be used once, on one phone. But that’s simply not true. Once created, the technique could be used over and over again, on any number of devices. In the physical world, it would be the equivalent of a master key, capable of opening hundreds of millions of locks — from restaurants and banks to stores and homes. No reasonable person would find that acceptable.
The government is asking Apple to hack our own users and undermine decades of security advancements that protect our customers — including tens of millions of American citizens — from sophisticated hackers and cybercriminals. The same engineers who built strong encryption into the iPhone to protect our users would, ironically, be ordered to weaken those protections and make our users less safe.
We can find no precedent for an American company being forced to expose its customers to a greater risk of attack. For years, cryptologists and national security experts have been warning against weakening encryption. Doing so would hurt only the well-meaning and law-abiding citizens who rely on companies like Apple to protect their data. Criminals and bad actors will still encrypt, using tools that are readily available to them.
A Dangerous Precedent
Rather than asking for legislative action through Congress, the FBI is proposing an unprecedented use of the All Writs Act of 1789 to justify an expansion of its authority.
The government would have us remove security features and add new capabilities to the operating system, allowing a passcode to be input electronically. This would make it easier to unlock an iPhone by “brute force,” trying thousands or millions of combinations with the speed of a modern computer.
The implications of the government’s demands are chilling. If the government can use the All Writs Act to make it easier to unlock your iPhone, it would have the power to reach into anyone’s device to capture their data. The government could extend this breach of privacy and demand that Apple build surveillance software to intercept your messages, access your health records or financial data, track your location, or even access your phone’s microphone or camera without your knowledge.
Opposing this order is not something we take lightly. We feel we must speak up in the face of what we see as an overreach by the U.S. government.
We are challenging the FBI’s demands with the deepest respect for American democracy and a love of our country. We believe it would be in the best interest of everyone to step back and consider the implications.
While we believe the FBI’s intentions are good, it would be wrong for the government to force us to build a backdoor into our products. And ultimately, we fear that this demand would undermine the very freedoms and liberty our government is meant to protect.
Tim Cook”
**************************************************************
Lawyers around the world should give Apple a standing ovation for its willingness to protect the privacy of users of their products as well as the privacy of those who communicate with them.
CLT
Posted by Cliff Tuttle| February 15, 2016 | © 2026
No. 1,246
Summary: If you are considering bidding on real estate in a private auction, start by asking for the rules in writing and a copy of the agreement of sale that will be signed by the successful bidder.

Image: reitips.com
A sheriff sale is a forced sale for the purpose of liquidating a judgment held by a creditor of the owner. The creditor generally starts the bidding with either the amount of the costs of the sale or the costs and taxes — the amount which must be paid first to taxing bodies and municipal providers of water, sewer. The creditor generally can bid up to the amount of the debt without paying anything additional, except costs and taxes. Tax sales have a similar procedure, but with a few more complications. But it is also a forced sale, conducted by a government official. The rules of sheriff sales, tax sales (and similar government and court-ordered sales) are well-established.
Private real estate auctions are voluntary sales conducted, not for a creditor, but for the owner. The owner may be a bank that previously foreclosed, but cannot find a buyer. The property may have been listed by a real estate broker for some time and failed to attract buyers.
Private real estate auctions are not new, but they seem to be increasing in frequency. Traditionally, they are conducted live by an auctioneer who takes bids from the audience in the usual way. However, today such auctions are increasingly conducted by on line auction houses with procedures similar to eBay. The bids may be accepted over a period of days. There are a number of on-line real estate auctioneers who can be easily found on Google.
If you are considering this investment opportunity, you should be aware that only a licensed Pennsylvania real estate broker is permitted to handle the sale of real property located in Pennsylvania. The purpose of licensing is to protect the consumer. The broker is expected to comply with Pennsylvania law. Every state has unique and frequently complex laws and regulations. National auction houses that do not have a Pennsylvania license probably are unaware of their responsibilities under our laws. Moreover, because a Pennsylvania broker is regulated by the Pennsylvania Real Estate Commission, he or she is subject to discipline for legal and ethical violations.
Although the property may be advertised “as is”, the owner may have a duty under Pennsylvania law to make comprehensive disclosures. A Pennsylvania broker will be aware of the seller’s obligations in a residential real estate transaction.
Equally important, you should ask to see a proposed agreement of sale before placing a bid. This is extremely important. Without an agreement setting forth the terms and conditions of the sale, it will be extremely difficult, maybe impossible, to get your money back. Or worse, the agreement could state that the deposit is non-refundable and that failure by the buyer to close for any reason is a breach of contract. It could permit the seller to sue for specific performance (requiring you to complete the transaction) and enable the seller to collect damages for various reasons, like delay.
Although you may ultimately prevail in court, that ordeal will probably be an expensive experience.
The agreement of sale should also provide for payment of all existing liens from the seller’s proceeds and pro-ration of current taxes and other obligations of the property. And it should permit the buyer to walk away, with the hand money, if the seller cannot give good title, free and clear of liens and encumbrances, as would be insured by a title insurance company without non-standard title exceptions.
There are a number of title issues that are important when a property has been through mortgage foreclosure. Junior lien holders are entitled to formal notice of the sheriff’s sale and the documentation filed by the plaintiff prior to the sale must conform to specific requirements. Failure to document proper notice could mean that the junior lien is not discharged. This would in turn require that the sheriff sale be conducted again or that the lucky junior lien holder be paid something to release the lien.
Another problem, easily overlooked, is that the property may still be occupied by the former owner or a tenant. Such a dilemma is not unusual. If the occupant does not leave voluntarily, evicting the former property owner or tenant may require additional legal action. Such title problems are usually expensive and time consuming. When they occur, the buyer should have the opportunity to terminate the deal and walk way, together with hand money.
CLT
Posted by Cliff Tuttle| February 12, 2016 | © 2026
 No. 1,245
No. 1,245
Summary: Trump’s self-funded campaign does not insure against contributor’s influence because Trump has the cause and effect equation backwards.
George Washington, whom we celebrate this President’s Day, was once reputed to be the wealthiest man in America. If so, his wealth consisted almost entirely in non-fungible frontier land, including a large swath of it in Western Pennsylvania.
He and most of the founding fathers served during the Revolution and the early days of the Republic without pay. This was the practical consequence of the inability of the pre-constitutional central government to levy taxes. But it also reflected the ideal of public service in Athenian Democracy and the Roman Republic, which Washington’s contemporaries read about in Plutarch’s Lives. Franklin and others advocated public service without pay at the Constitutional Convention, a proposal that was rightly rejected.
While many of the founding fathers endured severe financial sacrifice in order to serve, some of them couldn’t afford it — or barely could. Washington complained in his diary about the burden of feeding an endless procession of house guests at Mt. Vernon. Jefferson was pressed into near bankruptcy, with Congress providing a measure of relief by purchasing his library to found the Library of Congress.
Today, nearly all of the 2016 presidential candidates could easily serve eight years without drawing a government pay check. Forbes Magazine indicates that most have a net worth in the millions and, of course,one in the billions.
But a candidate who is so rich that he does not need to raise campaign funds is a novelty. Donald Trump says that he is not beholden to special interests, since he doesn’t accept their money. So far, he has had a free ride on this preposterous statement. Does this guaranty some kind of non-partisanship or impartiality in government?
Hardly. Mr. Trump has loudly declared his position on certain issues, such as immigration, trade, gun control and terrorist organizations. The positions that he has expressed are anything but nonpartisan. If he were accepting contributions, the interest groups who will benefit by his policy preferences would want to help to assure his re-election. In other words, Trump has reversed the cause and effect of political influence. In most cases, the candidate becomes known for certain policy preferences and contributors donate to help their political allies get elected. The candidate doesn’t change his position in response to contributions, the contributors help elect the candidates whose declared positions they favor.
CLT
Posted by Cliff Tuttle| February 7, 2016 | © 2026
No. 1,244
Several American lawyers who are still practiced until age 100 and beyond gave the same reason: once you stop working, you die.
Read it for yourself:
Murray H. Schusterman, Fox Rothschild, Philadelphia.
Jack Borden, Weatherford Texas
Richard Bird, Salt Lake City, Utah
and here’s a 95 year-old Solicitor from Dublin, Ireland.
Something to think about.
CLT
« go back —
keep looking »